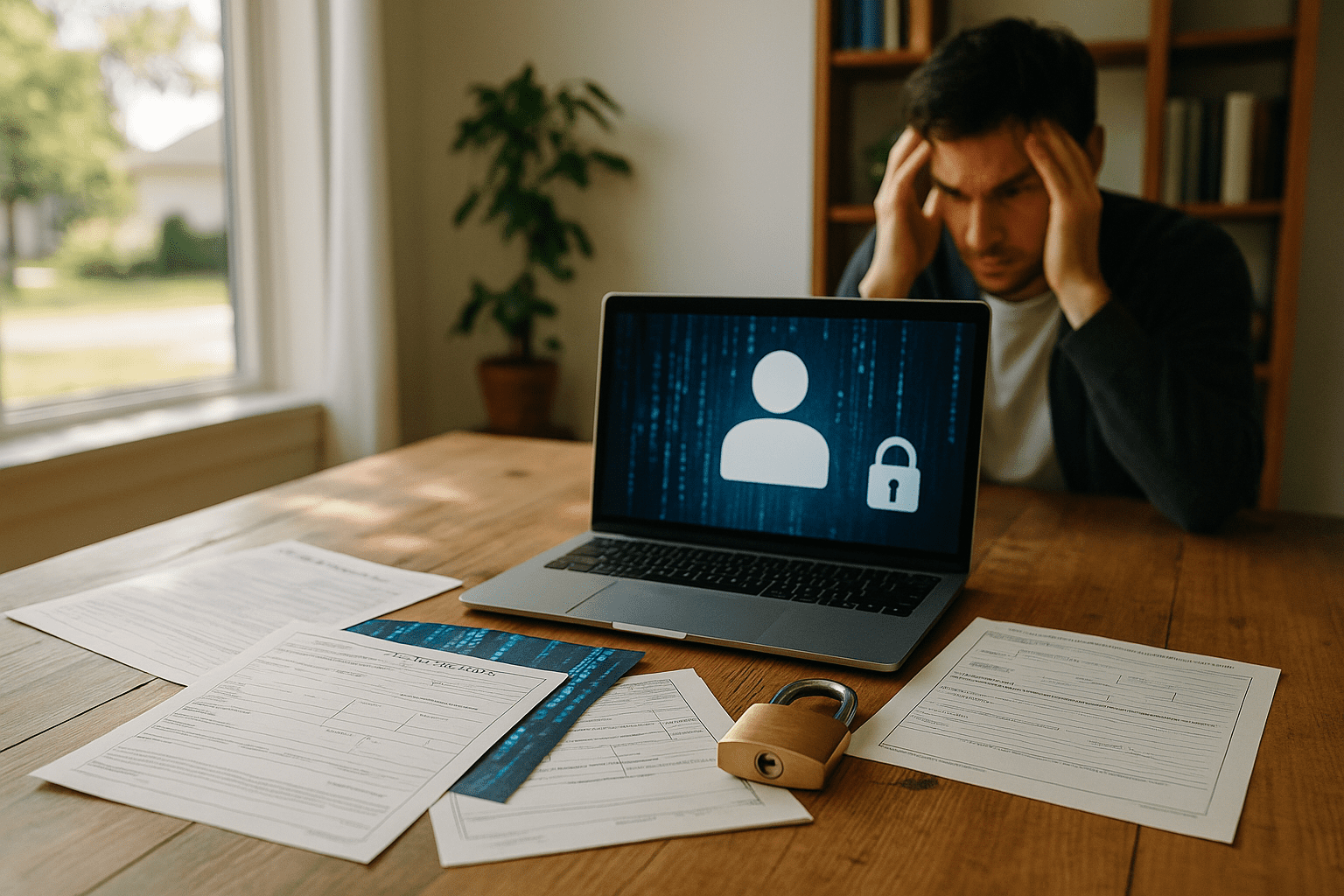
The term digital identity theft often brings to mind abstract threats lurking in the shadows of the internet: hackers cracking passwords, account breaches, or phishing emails promising quick access to your data. While these incidents are common and real, looking at public records can illuminate how these digital breaches actually translate into tangible consequences for people. Public records, after all, contain a trove of personal information that feeds into the digital identities we live with every day.
How Public Records Reflect Real-World Data Vulnerabilities
Public records such as court filings, property transactions, and professional licenses exist openly because of transparency laws or state requirements. However, the openness that serves civic purposes also makes these records a frontline for digital identity risks. When digital identity theft happens, attackers often piece together data from these easily accessible sources alongside stolen credentials to create detailed profiles. This means that someone might not only learn your name and address but trace your address history, employment, or even family connections from public data.
Consider how many people do people searches online to reconnect or verify background information. This behavior itself underscores how identities are composed of linked data points scattered across many public and private sources. The durability and accessibility of these records mean that once personal information is exposed or stolen digitally, it can travel far and wide, making containment difficult.
A Fragmented Picture That’s Hard to Patch
One of the most striking features revealed by examining public records is how fractured identity data is. There is no single master file of a person’s identity. Many agencies, local courts, property offices, and licensing boards each maintain parts of an individual’s identity puzzle. Digital identity thieves exploit this fragmentation by extracting bits from multiple sources to impersonate or defraud.
This makes protecting digital identities trickier than simply guarding a single password or account. Understanding how these records link forward and backward in time calls attention to how data legacy impacts current identity safety. For instance, a court record revealing a past legal dispute might resurface years later combined with a stolen Social Security number, amplifying risk.
Efforts to secure digital identities must therefore reckon with how public records can unintentionally assist identity thieves by preserving durable and accessible trails. The persistence of these records contrasts sharply with the transient nature of digital credentials, which can be changed or revoked.
The Double-Edged Sword of Transparency and Accessibility
Public records serve many functions that benefit society: transparency, accountability, and access to important civic information. But these benefits come with trade-offs. Transparency helps journalists, investigators, and everyday citizens understand matters that affect communities, but it can also expose sensitive information that criminals use.
In the age of the internet, information that once required in-person requests or physical visits now can be aggregated and searched online with ease. This shift means that digital identity theft is less about obscure hacks and more often about easily accessible public data combined with stolen private credentials.
Some jurisdictions are beginning to reconsider what personal details should be readily available online and which need more stringent protections. Additionally, people search companies and data brokers collect and compile information from these public records, adding layers of aggregation that can both help and harm individuals depending on how they are used.
Patterns in Breaches Echo Real-World Record Behavior
Looking through data breach reports and digital identity theft cases, one can see patterns that reflect public records behavior. It is common for stolen data to include addresses, past employers, and even family member information-elements often commonly found in public records. This overlap suggests that attackers are not merely guessing identity details but methodically assembling them using real-world documentation.
This underlines a need for deeper awareness and education around how various data sources fit together. For example, seeing a court docket with your name alongside a stolen credit card number could trigger serious financial damage. Recognizing what public records exist and how they are linked can help those affected respond more effectively.
Some helpful resources outline how to check if your information appears in breach collections or to monitor identity use over time. Though these tools can never be perfect due to the nature of data flows, they hint at ways to engage with the reality of digital identity safety in a world intertwined with public record systems.
Beyond the Technical: The Human Side of Identity Theft
Ultimately, digital identity theft, when viewed through public records, reminds us that these are not simply lines of code or database entries but represent lived histories and relationships. A property record denotes a home someone has invested in. A court case might reflect a personal hardship or dispute. Address histories often reflect family dynamics or major life changes.
Understanding the interplay between digital breaches and public records leads to appreciating the stakes involved in identity theft. Recovery is not only about securing accounts but also about restoring trust and dignity tied to one’s name and story documented in public files.
This observation invites caution while navigating the internet and civic record systems alike. Being aware of what information you leave visible or accessible, and how it might be combined with other data, can help frame better protections.
For individuals working to untangle the messy consequences of digital identity theft, public records can be both a source of vulnerability and an unexpected resource to piece together what happened. Over time, learning how to interpret these records alongside digital alerts can become an essential part of managing identity in the modern era.
Understanding the reality of digital identity theft through the lens of public records gives a fuller picture of risks and responses, one rooted in the complex, interconnected world we navigate today.
Further reading on protecting personal identity and understanding public records is available through resources like the Federal Trade Commission’s IdentityTheft.gov site, which offers practical recovery plans. For those curious about how data aggregation happens, the Privacy Rights Clearinghouse provides essays on public records and privacy. The USA.gov resource page also clarifies what types of public records are accessible and their typical uses.
These perspectives illustrate that digital identity theft is a multifaceted problem extending beyond online accounts into realms where traditional records hold sway.
Sources and Helpful Links
- Federal Trade Commission’s IdentityTheft.gov – Official government resource for identity theft help and recovery methods.
- Privacy Rights Clearinghouse on Public Records – Explains privacy concerns related to public record availability.
- USA.gov Public Records – Guide to public records types and access across US government institutions.